In this blog, I will explain the steps involved in creating a hybrid mobile app using Oracle JET
Follow the below steps to get started :
1) Install Node.js on your development machine. Download from here https://nodejs.org/en.After installation, you should be able to run npm commands.
2) Run cmd as Administrator and then run the below commands to install various modules via npm :
There are two ways to create Oracle JET Hybrid mobile application
(i) For ojet 4.1 or later use the below steps:
You can just install oracle-jet cli and Cordova to get started
npm install -g @oracle/ojet-cli cordova
@oracle-jet cli contains the oraclejet generator, so there is no need to install it separately. Also to install a specific version of the oracle jet-cli use @version
eg.
npm install -g @oracle/ojet-cli@5.0.0 cordova
You can build and serve your app using ojet command-
Build JET app for android:
ojet build android
Serve JET app for android:
ojet serve android
(ii) For ojet 2.0 use the below steps:
a. Install Yeoman :
npm install -g yo
Enter npm list –g yo to verify that the command succeeded. If the package isn’t listed, scroll through the install command output to locate the source of the failure.
b. Install Grunt :
npm install -g grunt-cli
c. Install Bower :
npm install -g bower
d. Install Cordova :
npm install -g cordova
e. Install generator-oraclejet
npm install -g generator-oraclejet
Note: you can check the above installed packages and their versions using
npm list -g --depth=0
3) Install Mobile tooling to deploy, debug on devices
Install Android Tools
To develop applications for the Android platform, you must install the Android SDK and create Android Virtual Devices (AVDs) so that you can run your app in the Android emulator.
Use Cordova’s Android Platform Guide to install the Android tools on your machine.
Install iOS Tools
Use Cordova’s iOS Platform Guide, install Xcode and the iOS Simulator on your IOS machine. This step is sufficient for developing iOS applications and testing it.
Create a simple hybrid mobile project using ojet command
ojet create myHybridApp --hybrid --appid="com.oracle.myApp" --appname="MyHybridApp" --platforms=ios,android --template=navdrawer
You can build and serve your app using ojet command-
Build JET app for the Android platform:
ojet build android
Serve JET app for android platform:
ojet serve android




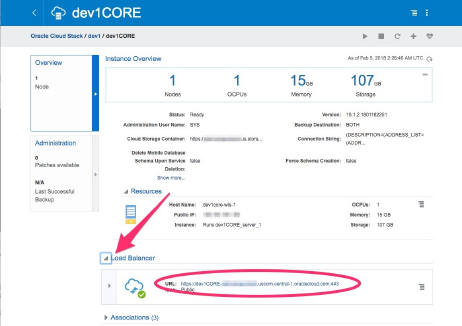
 to open the side menu and select
to open the side menu and select  to get to Storage Classic.
to get to Storage Classic.